Security service
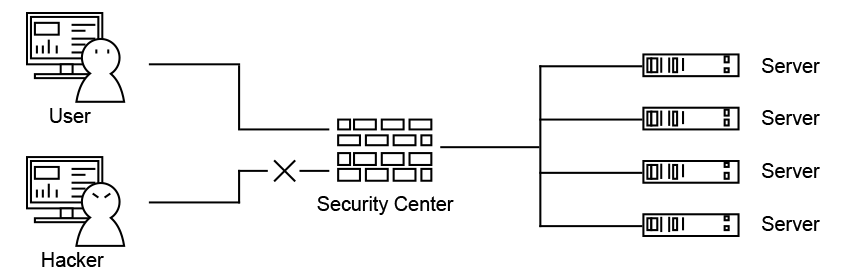
Prepare for changes and threats with a firewall
Changes in computing environment
· High performance of personal terminals
· High bandwidth of network transmission media
· Diversification of network terminals
Increasing security threats
· Neutralization of intellectual assets due to DDoS
· Malicious data inflow and confidential information leakage
· Difficulty responding to various security threats
Recent security threat trends
· Intrusion through public Internet sessions used by external/internal users
· Internal data leakage through P2P, messenger, SNS, etc.
Protect key assets at the top of the network asset structure
Firewall
Zone-based firewall,
User authentication-based access control
IPS
PCRE support, bypass detection attack,
Snort rule format
Anti-DDoS
Flooding, Scan/Sweep,
Protocol/Traffic Anomaly, automatic learning
Content-Filter
Application control, Web filter,
Custom URL Filter
Qos
Bandwidth-based guarantees/limits,
PPS Limits
Anti-Virus
Stream/File based Virus Detection
Anti-Spam
RBL support
Block access by unauthorized users
* Provides an optimal security environment according to the business environment of each company, including IDC-based web services, services containing personal information, and all PCs in Office Zone.
Security experts from iSolution Co., Ltd. provide support
24/365 technical support
Establishing a response system
Various customer references
Based operational know-how
Optimal network
Configuration suggestions
Policy processing and result notification
Vulnerable policy guide provided




